Kittur, L. J., Mehra, R. & Chandavarkar, B. R. The dependency of healthcare on security: Issues and challenges. In ICCCE 2020: Proceedings of the 3rd International Conference on Communications and Cyber Physical Engineering. 119–129. (Springer Nature Singapore, 2020). https://doi.org/10.1007/978-981-15-7961-5_12
Folasole, A., Adegboye, O. S., Ekuewa, O. I. & Eshua, P. E. Security, privacy challenges and available countermeasures in electronic health record systems: A review. Eur. J. Electr. Eng. Comput. Sci. 7 (6), 27–33. (2023).
Google Scholar
Rai, A. Case studies on disproportionate impact of cyberattacks in the healthcare sector. J. High. School Res. (2024).
Google Scholar
Khan, M. Healthcare cybersecurity: A mini review on recent incidents and preventive strategies. SSN J. Manage. Technol. Res. Commun. (2024).
Google Scholar
Triplett, W. Ransomware attacks on the healthcare industry. J. Bus. Technol. Leadersh. 4 (1), 1–13. (2022).
Google Scholar
Cartwright, A. J. The elephant in the room: cybersecurity in healthcare. J. Clin. Monit. Comput. 37 (5), 1123–1132. (2023).
Google Scholar
Ifinedo, P. Understanding information systems security policy compliance: an integration of the theory of planned behavior and the protection motivation theory. Comput. Secur. 31 (1), 83–95. (2012).
Google Scholar
Hearth, T. & Rao, H. R. Protection motivation and deterrence: A framework for security policy compliance in organizations. Eur. J. Inform. Syst. 18 (2), 106–125. (2009).
Google Scholar
Workman, M., Bommer, W. H. & Straub, D. Security lapses and the omission of information security measures: A threat control model and empirical test. Comput. Hum. Behav. 24 (6), 2799–2816. (2008).
Google Scholar
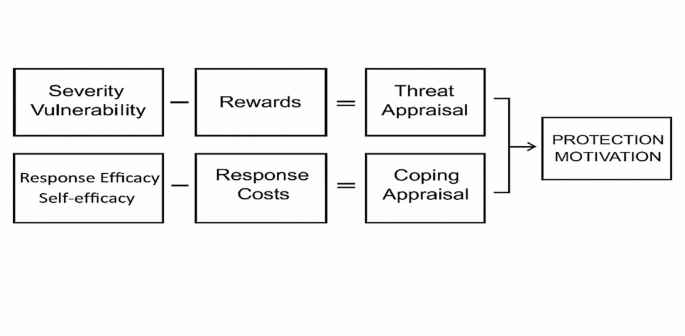
Rogers, R. W. A protection motivation theory of fear appeals and attitude change1. J. Psychol. 91 (1), 93–114 (1975).
Google Scholar
Maddux, J. E. & Rogers, R. W. Protection motivation and self-efficacy: A revised theory of fear appeals and attitude change. J. Exp. Soc. Psychol. 19 (5), 469–479. (1983).
Google Scholar
Jalali, M. S. & Kaiser, J. P. Cybersecurity in hospitals: a systematic, organizational perspective. J. Med. Internet. Res. 20 (5), e10059. (2018).
Google Scholar
Moody, G. D., Siponen, M. & Pahnila, S. Toward a unified model of information security policy compliance. MIS Q. 42 (1), 285–A22. (2018).
Google Scholar
Towbin, R. S. A Protection Motivation Theory Approach To Healthcare Cybersecurity: A Multiple Case Study (Northcentral University, 2019).
Lebek, B., Uffen, J., Neumann, M., Hohler, B., Breitner, H. & M Information security awareness and behavior: a theory-based literature review. Manage. Res. Rev. 37 (12), 1049–1092 (2014).
Google Scholar
Menard, P., Warkentin, M. & Lowry, P. B. The impact of collectivism and psychological ownership on protection motivation: A cross-cultural examination. Computers Secur. 75, 147–166. (2018).
Google Scholar
Ma, X. IS professionals’ information security behaviors in Chinese IT organizations for information security protection. Inf. Process. Manag. 59 (1), 102744. (2022).
Google Scholar
Floyd, D. L., Prentice-Dunn, S. & Rogers, R. W. A meta‐analysis of research on protection motivation theory. J. Appl. Soc. Psychol. 30 (2), 407–429. (2000).
Google Scholar
Van Bavel, R., Rodríguez-Priego, N., Vila, J. & Briggs, P. Using protection motivation theory in the design of nudges to improve online security behavior. Int. J. Hum. Comput. Stud. 123, 29–39. (2019).
Google Scholar
Liang, H. & Xue, Y. Avoidance of information technology threats: A theoretical perspective. MIS Q. 71–90. (2009).
Lee, Y. & Larsen, K. R. Threat or coping appraisal: determinants of SMB executives’ decision to adopt anti-malware software. Eur. J. Inform. Syst. 18 (2), 177–187. (2009).
Google Scholar
Hwang, I., Kim, D., Kim, T. & Kim, S. Why not comply with information security? An empirical approach for the causes of non-compliance. Online Inf. Rev. 41 (1), 2–18. (2017).
Google Scholar
Nelson, R. Factors that Influence Medical Professionals’ Noncompliance with Organizational Mobile Device Security Policies (Doctoral Dissertation, Capella University, 2019).
Haag, S., Siponen, M. & Liu, F. Protection motivation theory in information systems security research: A review of the past and a road map for the future. ACM SIGMIS Database: DATABASE Adv. Inform. Syst. 52 (2), 25–67. (2021).
Google Scholar
Li, W., Liu, R., Sun, L., Guo, Z. & Gao, J. An investigation of employees’ intention to comply with information security system—A mixed approach based on regression analysis and FsQCA. Int. J. Environ. Res. Public Health. 19 (23). (2022).
Johnston, A. C., Warkentin, M. & Siponen, M. An enhanced fear appeal rhetorical framework. MIS Q. 39 (1), 113–134. (2015).
Google Scholar
Schneider, M. Protection Motivation Theory Factors that Influence Undergraduates to Adopt Smartphone Security Measures (Doctoral Dissertation, Capella University, 2020).
Tsai, H. Y. S. et al. Understanding online safety behaviors: A protection motivation theory perspective. Computers Secur. 59, 138–150. (2016).
Google Scholar
Khan, N. F., Murtaza, H., Malik, K., Mahmood, M. & Asadi, M. A. Explanatory and predictive analysis of smartphone security using protection motivation theory: a hybrid SEM-AI approach. Inform. Technol. People. 38 (4), 2041–2068 (2025).
Google Scholar
Warkentin, M., Johnston, A. C., Shropshire, J. & Barnett, W. D. Continuance of protective security behavior: A longitudinal study. Decis. Support Syst. 92, 25–35. (2016).
Google Scholar
Thompson, N., McGill, T. & Narula, N. No point worrying’–The role of threat devaluation in information security behavior. Comput. Secur. 143. (2024).
Burns, A. J., Posey, C., Roberts, T. L. & Lowry, P. B. Examining the relationship of organizational insiders’ psychological capital with information security threat and coping appraisals. Comput. Hum. Behav. 68, 190–209 (2017).
Google Scholar
Almansoori, A., Al-Emran, M. & Shaalan, K. Exploring the frontiers of cybersecurity behavior: A systematic review of studies and theories. Appl. Sci. 13 (9), 5700. (2023).
Google Scholar
Bandura, A. Self-Efficacy: The Exercise of Control (Macmillan, 1997).
Bandura, A. Social Foundations of Thought and Action (Englewood Cliffs, 1986).
Borgert, N. et al. Self-efficacy and security behavior: Results from a systematic review of research methods. In Proceedings of the 2024 CHI Conference on Human Factors in Computing Systems. 1–32. (2024). https://doi.org/10.1145/3613904.3642432
Vance, A., Siponen, M. & Pahnila, S. Motivating IS security compliance: insights from habit and protection motivation theory. Inf. Manag. 49 (3–4), 190–198. (2012).
Google Scholar
Mortada, E., Abdel-Azeem, A., Al Showair, A. & Zalat, M. M. Preventive behaviors towards Covid-19 pandemic among healthcare providers in Saudi Arabia using the protection motivation theory. Risk Manag. Healthc. Policy 685–694. (2021).
Sreenath, S. S., Hewitt, B. & Sreenath, S. Understanding security behaviour among healthcare professionals by comparing results from technology threat avoidance theory and protection motivation theory. Behav. Inform. Technol. 44 (2), 181–196. (2024).
Google Scholar
Sari, P. K., Handayani, P. W., Hidayanto, A. N., Yazid, S. & Aji, R. F. Information security behavior in health information systems: A review of research trends and antecedent factors. In Healthcare. Vol. 10(12) 2531. (MDPI, 2022). https://doi.org/10.3390/healthcare10122531
Yeng, P. K., Fauzi, M. A. & Yang, B. A comprehensive assessment of human factors in cyber security compliance toward enhancing the security practice of healthcare staff in paperless hospitals. Information 13 (7), 335. (2022).
Google Scholar
Yeng, P. K., Fauzi, M. A. & Yang, B. Assessing the effect of human factors in healthcare cyber security practice: An empirical study. In Proceedings of the 25th Pan-Hellenic Conference on Informatics. 472–476. (2021). https://doi.org/10.1145/3503823.3503909
Kiran, U., Khan, N. F., Murtaza, H., Farooq, A. & Pirkkalainen, H. Explanatory and predictive modeling of cybersecurity behaviors using protection motivation theory. Computers Secur. 149, 104204 (2025).
Google Scholar
Khan, N. F., Ikram, N., Murtaza, H. & Javed, M. Evaluating protection motivation based cybersecurity awareness training on Kirkpatrick’s model. Computers Secur. 125, 103049 (2023).
Google Scholar
Simon, J., Watson, S. J., & van Sintemaartensdijk, I. Response-efficacy messages produce stronger passwords than self-efficacy messages… for now: A longitudinal experimental study of the efficacy of coping message types on password creation behaviour. Comput. Hum. Behav. Rep. 17, 100615 (2025).
van’t Hoff-de Goede, M. S., Leukfeldt, E. R., van de Weijer, S. G. A. & van der Kleij, R. Does protection motivation predict self-protective online behaviour? Comparing self-reported and actual online behaviour using a population-based survey experiment. Computers Hum. Behav. Rep. 18, 100649 (2025).
Google Scholar
Khan, N. F., Ikram, N. & Saleem, S. Effects of socioeconomic and digital inequalities on cybersecurity in a developing country. Secur. J. 1 (2023).
Khan, N. F., Ikram, N. & Saleem, S. Digital divide and socio-economic differences in smartphone information security behaviour among university students: empirical evidence from Pakistan. Int. J. Mobile Commun. 22 (1), 1–24 (2023b).
Google Scholar
Kanimozhi, R., Padmavathi, V. & Ramesh, P. S. Perceived digital threats influencing smartphone use among the aging population. Sci. Rep. 15 (1), 27813 (2025).
Google Scholar
Khadka, K. & Ullah, A. B. Human factors in cybersecurity: an interdisciplinary review and framework proposal. Int. J. Inf. Secur. 24, 119. (2025).
Google Scholar
Zou, Y. et al. Encouraging users to change breached passwords using the protection motivation theory. ACM Trans. Computer-Human Interact. 31 (5), 1–45 (2024).
Google Scholar
Weber, A. S. et al. Systematic thematic review of e-health research in the Gulf Cooperation Council (Arabian Gulf): Bahrain, Kuwait, Oman, Qatar, Saudi Arabia and United Arab Emirates. J. Telemed. Telecare. 23, 452–459. (2017).
Google Scholar
Al-Azri, M. H., Al-Belushi, R., Al-Mamari, M., Davidson, R. & Mathew, A. C. Knowledge and health beliefs regarding sickle cell disease among Omanis in a primary healthcare setting: cross-sectional study. Sultan Qaboos Univ. Med. J. 16 (4), e437. (2016).
Google Scholar
Al-Farsi, O. A. et al. A study on knowledge, attitude, and practice towards premarital carrier screening among adults attending primary healthcare centers in a region in Oman. BMC Public. Health. 14, 1–7. (2014).
Google Scholar
Qoronflesh, M. W., Essa, M. M., Alharahsheh, S. T., Al-Farsi, Y. M. & Al-Adawi, S. Autism in the Gulf states: A regional overview. Front. Bioscience-Landmark. 24 (2), 334–346. (2019).
Google Scholar
MOH. MOH Annual Report. (2020).
Walliman, N. Research Methods: The Basics (Routledge, 2011).
Oniwinde, B. The essence of compliance is making choices. Social Sci. Res. Netw. (2024).
Google Scholar
Lowry, P. B. & Moody, G. D. Proposing the control-reactance compliance model CRCM to explain opposing motivations to comply with organisational information security policies. Inform. Syst. J. 25 (5), 433–463. (2015).
Google Scholar
Bozeman, B. Rules compliance behavior: A heuristic model. Perspect. Public. Manage. Gov. 5 (1), 36–49. (2022).
Google Scholar
link