A new Microsoft Threat Intelligence report highlights how the rapidly evolving threat landscape is prompting a rethinking of traditional defenses. The adoption of AI by both defenders and threat actors is creating new challenges for security organizations, which must quickly adapt systems, understand emerging threats, and equip teams with the knowledge to keep up. Cyber threats are increasingly shaping geopolitical conflicts and criminal activities, expanding the scope of responsibility for defenders. While AI will play a critical role in addressing these challenges, the industry must approach this new paradigm with caution.
“We are living through a defining moment in cybersecurity,” Amy Hogan-Burney, Microsoft’s corporate vice president for customer security and trust, and Igor Tsyganskiy, corporate vice president and chief information security officer at Microsoft, wrote in the report titled ‘Microsoft Digital Defense Report 2025: Lighting the path to a secure future. “As digital transformation accelerates, supercharged by AI, cyber threats increasingly challenge economic stability and individual safety. Cyber threats are rapidly evolving from technical problems affecting business to events impacting all aspects of our society.”
They point out that adversaries, whether nation-states, criminal syndicates, or commercial cyber mercenaries, are leveraging emerging technologies to attack with both greater volume and more precision than ever before, often by exploiting the trust that underpins our digital lives. International collaboration among defenders will be critical to define new coordinated defenses and set new international norms that enforce consequences for cyberattacks targeting the global critical infrastructure or essential services.
“For security leaders, the imperative is clear: cybersecurity must be a priority, embedded into the fabric of organizational strategy and addressed regularly as part of risk management,” the Microsoft executives detailed. “Global partnerships across industry peers and even competitors must be established to coordinate and collaborate on defenses against common adversaries. Traditional perimeter defenses are no longer sufficient. Resilience must be designed into systems, supply chains, processes, and governance. New types of threats will emerge with increasing frequency; being informed and prepared is critical.”
In its 85-page 2025 digital defense report, Microsoft identified that adversaries are increasingly using generative AI for activities such as scaling social engineering, automating lateral movement, discovering vulnerabilities, and evading security controls. Autonomous malware and AI-powered agents are adapting their tactics in real-time, posing a challenge for defenders to shift from static detection to behavior-based, anticipatory defense. At the same time, AI systems themselves have become high-value targets. Adversaries are using techniques like prompt injection and data poisoning to exploit AI models and systems, which can lead to unauthorized actions, data leaks, theft, or reputational damage.
Campaigns now rely on multi-stage attack chains that combine social engineering with technical exploits. One such technique, ‘ClickFix,’ tricks users into executing malicious code, bypassing traditional phishing defenses. Additionally, device code phishing has emerged as a new method of gaining access, used by both cybercriminals and nation-state actors.
In today’s cybercrime economy, adversaries are increasingly logging into systems rather than breaking in. Infostealers are used to collect credentials and tokens, which are then sold on the dark web. This often leads to follow-on activities such as ransomware, data exfiltration, and extortion. As a result, organizations infected with infostealers face a higher risk of future breaches.
Nation-state cyber activity continues to rise, particularly targeting the communications, research, and academic sectors. These operations are primarily aimed at gathering intelligence through cyber espionage, complementing traditional intelligence methods. Additionally, nation-state actors are accelerating the use of AI to enhance their cyber and influence operations, making them more scalable, advanced, and targeted.
“AI now plays a transformative role in our defense strategy, enabling us to synthesize vast data sets, detect novel threats, and respond in moments, not hours—empowering defenders to anticipate and disrupt attackers, to protect individuals, organizations, or critical infrastructure,” the report identified. “Yet, we recognize that no single organization can see or solve every challenge alone. By sharing our insights, lessons learned, and best practices in this report, we aim to strengthen collective cyber resilience and empower defenders everywhere.”
Microsoft’s 2025 digital defense report identified that as critical infrastructure becomes increasingly dependent on digital technology, nation-state cyber operations targeting these systems cannot be permissible; in particular those prepositioning for disruptive or destructive cyberattacks in case of future conflicts. Defensive actions alone to protect critical infrastructure are unlikely to deter nation-state threat adversaries. These are politically motivated activities that must be addressed with political solutions as well. To protect critical infrastructure, political institutions, and civilian systems, governments must build frameworks that signal credible and proportionate consequences for malicious activity that violate international rules.
Over the past year, there has been a marked increase in recognition of the need for such cyber deterrence, with governments and industry aligning more closely to response to malicious activity.
NATO has advanced coalition-based attribution frameworks and is exploring collective countermeasures in response to cyberattacks. In July, the alliance released a statement recognizing and condemning malicious cyber activities attributed to Russia by member states. The U.S. administration has issued strong public statements and indictments tied to cyber operations and has publicly attributed cyberattacks in coordination with allies and partners. The EU is increasingly leveraging its Cyber Diplomacy Toolbox and sanctions regime to hold bad actors accountable, though implementation remains uneven.
Looking ahead, these are important foundations to build upon. To further strengthen a cyber deterrence framework, like-minded governments should work to regularize public attributions. States should more consistently issue public attribution statements, leveraging insights from other governments and partners in the private sector and establishing a more uniform process for doing so. Such statements should always indicate if international laws or norms were violated during a cyber incident.
States should make clear they will impose increasingly severe consequences in response to a spectrum of malicious nationstate cyber activity, ranging from espionage to prepositioning to disruptive and or destructive cyber operations. They must impose diverse consequences. Responses to nation-state cyberattacks should not be constrained to the cyber domain or prescribed in a one-sizefits-all model. Different threat actors will be deterred by different consequences. These could include economic measures, diplomatic sanctions, naming and shaming, posturing, or targeted declassification.
The 2025 digital defense report also recognized that private companies are not in the position to hack back against malicious nationstate actors independently, and doing so can risk unintended escalation and harm. While industry can support attributions and partner with government to take action, imposing consequences for internationally wrongful behavior by states will always need to be led by governments.
Many of the most prolific ransomware groups avoid consequences by targeting victims in other countries while their own governments turn a blind eye. Whether they are state-affiliated groups or their government simply ignores their activity, the result is the existence of ‘safe haven’ states that enable ransomware attacks abroad and violate international norms of due diligence which oblige governments to take action to prevent illegal cyber activity within their borders.
As a result, addressing ransomware operations requires a more coordinated international effort and political pressure that holds governments accountable for both direct and indirect support of ransomware attacks. Designating state sponsors of ransomware, for example, similar to state sponsors of terror, with associated stigmas and penalties, is one way to incentivize states to confront ransomware groups operating within their borders.
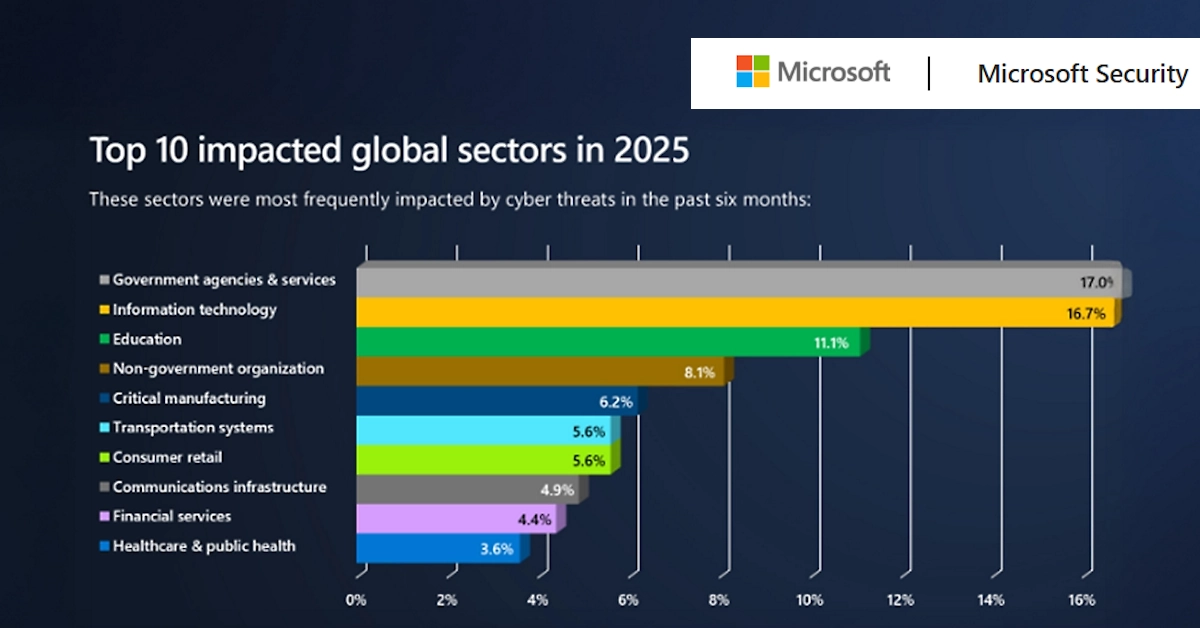
Microsoft’s 2025 digital defense report detailed that nation-state cyber activity this year prioritized espionage against traditional intelligence targets, including IT, research and academia, government, and think tanks/ NGOs. “A minority of attacks, for example against the Defense Industrial Base, sought to steal proprietary information for economic advantage. An even smaller number of attacks had other goals, including sabotage and ransom. A major threat that emerged this year was the discovery of the magnitude of North Korea’s program to stealthily embed remote workers at organizations around the world.”
The report revealed that the growing threat has multiple facets, including the risk of sanctions violation, espionage, extortion, and sabotage. In line with geopolitical hotspots and longstanding intelligence priorities, the primary geographical targets of nation-state activity this year were in Israel, the U.S., and the United Arab Emirates. Predictably, Ukraine was also an extreme focus for Russian actors.
The Microsoft 2025 digital defense report recommended that cybersecurity should be managed at the boardroom level, treating it as a business risk equal to financial or legal challenges. Corporate boards and CEOs need to understand the security weaknesses of their organization and track metrics such as multifactor authentication coverage, patch latency, incident counts, and incident response time to gain a comprehensive view of vulnerabilities and preparedness for potential incidents. The report emphasizes prioritizing the protection of identities, as identity remains the top attack vector. Organizations should enforce phishing-resistant multifactor authentication across accounts, including administrative accounts.
It also highlights the importance of investing in people, not just tools. Cybersecurity is a whole-of-organization responsibility, and organizations should upskill their workforce and consider incorporating security into performance reviews. Culture and readiness, alongside technology, are key factors in both an organization’s defenses and its overall resilience.
Defending the perimeter is critical, as a third of attackers rely on crude tactics to exploit an organization’s exposed footprint. They often target not only internal systems but also trusted vendors and supply chains, including perimeter web-facing assets, external remote services, and supply chain connections. Understanding the full scope of the perimeter, auditing access granted to trusted partners, and patching exposed systems increases the effort required for attackers to succeed.
Organizations should combine knowledge of their exposure footprint with overall risk awareness to develop a proactive plan for responding to potential breaches. Security controls should be tied to business risks in terms that boards can understand. Since a breach is a matter of when, not if, incident response plans should be developed, tested, and practiced, including specific scenarios for ransomware attacks, which remain among the most disruptive and costly threats to operations. Rapid isolation of systems and revocation of credentials are essential components of preparedness.
As the cloud has become a primary target for adversaries, organizations must inventory every cloud workload, application programming interface, and identity, while monitoring for rogue virtual machines, misconfigurations, and unauthorized access. Proactive enforcement of application governance, conditional access policies, and continuous token monitoring is also critical to maintaining security in cloud environments.
Resilience and recovery are essential, as breaches are increasingly inevitable. Backups should be tested, isolated, and restorable, and organizations should maintain clean rebuild procedures for identity systems and cloud environments. Cyber defense relies on collaboration rather than individual effort. Sharing and receiving real-time threat data with peers, industry groups, and government agencies makes it more difficult for adversaries to achieve their objectives.
Organizations must also prepare for regulatory changes by aligning with emerging laws such as the EU Cyber Resilience Act or U.S. critical infrastructure mandates, which may require timely reporting of cyber incidents or adherence to Secure by Design practices. These regulations underscore the importance of prompt incident reporting and strengthened internal oversight of cybersecurity practices.
The 2025 digital defense report also callied upon organizations to begin planning for AI and quantum risks immediately. It is important to understand both the benefits and risks of AI within the organization and to adjust risk planning, attack surface exposure, and threat models accordingly. Preparation for a post-quantum cryptography (PQC) environment requires inventorying where encryption is used and developing a plan to transition to modern standards as they evolve.
link